6 Lessons Learned from the Biggest Data Breaches in US History
- Home
- 6 Lessons Learned from the Biggest Data Breaches in US History

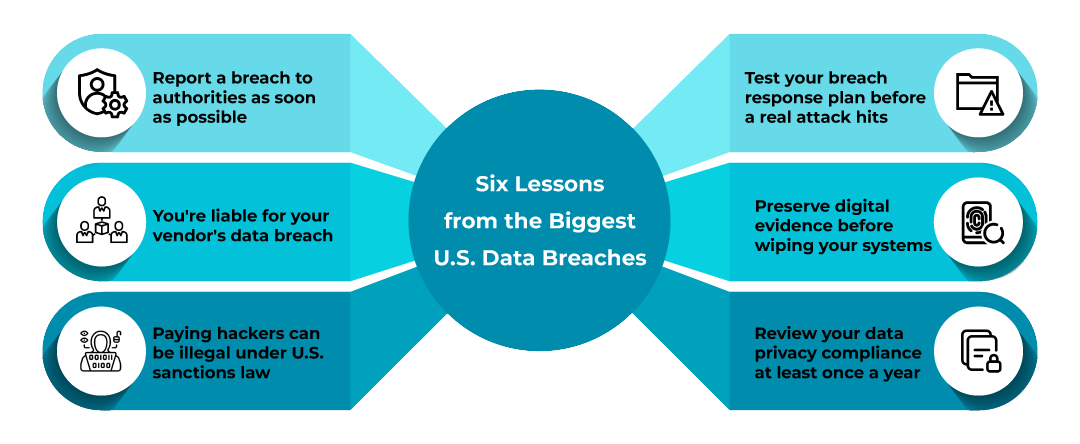
A data breach does not care how big your company is. It really does not care that your legal team is solid or that your IT department passed its last audit. What it actually cares about, and what attackers actively look for, is the gap between what your policies say and what actually happens on the ground. That gap has cost companies billions. And if you look closely at the most significant breaches of the past few years, the same hard lessons keep showing up.
We work with U.S. businesses on cyber incident response review, and we see the fallout firsthand. The regulatory exposure, the contract disputes, the litigation? We’ve seen it all. That’s why we believe that the legal consequences of a data breach are not an afterthought. They are front and center, often before the technical team has even finished their forensic analysis.
So let’s get into it. Six real, hard-earned lessons from the USA’s high-profile breaches with the legal and operational takeaways your business actually needs.
Lesson 1: Late Notification Is a Legal Liability, Not Just a PR Problem
Uber was under intense legal scrutiny in 2022. However, this was not only because of its 2016 breach; it was also because of the length of time it took to notify authorities and the public. Joe Sullivan, a former CSO, was found guilty of concealment and obstruction. This was not a technical failure. It was a breach notification failure.
Under laws such as HIPAA, state-level data protection laws, and the SEC’s new cybersecurity disclosure rules (effective December 2023), timely incident disclosure is a legal obligation rather than a judgment call. Most states have notification windows of 30 to 72 hours for certain categories of data. The FTC also monitors for deceptive practices around breach handling.
The takeaway? Your cyber incident response plan needs built-in legal escalation triggers. The moment a breach is suspected, legal counsel and your notification workflow should be activated, not after forensics are complete.
Lesson 2: Third-Party Vendors Are Your Risk, Too
A master class in third-party risk management—or rather, the absence of it—was provided by the 2023 MOVEit breach. The CL0p ransomware group exploited a zero-day vulnerability in Progress Software’s MOVEit file transfer tool, which had a cascading effect on over 2,500 organizations, including Shell, the BBC, and several federal agencies in the United States.
The legal aspect that most businesses overlook is that you are still accountable if your vendor is compromised and your customer information escapes. Your customers’ contracts are with you, not your vendor. Regulatory bodies go after the primary data controller.
This is why vendor due diligence and robust data processing agreements are not optional. Your agreements with third parties need to contain security audit provisions, notification of breaches, and indemnification provisions that are enforceable. If they don’t, change them.
Lesson 3: Ransomware Payment Decisions Have Legal Consequences
One of the worst healthcare data breaches in American history occurred at Change Healthcare in early 2024, and it is said that a ransom payment of about $22 million was required. Pharmacies, hospitals, and patients nationwide were impacted by the weeks-long crippling of UnitedHealth Group’s subsidiary.
But here’s what a lot of companies don’t fully grasp: paying a ransom can put you on the wrong side of U.S. law. OFAC (the Office of Foreign Assets Control) has made it very clear that if the ransomware group is on a sanctions list, paying them even unknowingly could result in civil penalties. And after paying, you still have to complete your regulatory breach reporting obligations. Payment does not buy you legal cover.
Before any ransom decision is made, legal counsel needs to be in the room. Full stop.
Lesson 4: A Data Breach Response Plan That Isn't Tested Is Just a Document
MGM Resorts’ 2023 attack took down reservations, hotel room keys, casinos, and ATMs for days. Estimated losses exceeded $100 million. What made it worse? The attacker reportedly used a social engineering attack, impersonating an employee to IT support, to get in. The technical side of the breach was almost secondary.
MGM had policies. They had teams. But in the moment, the incident response plan did not hold. Why? Because cybersecurity tabletop exercises, where you actually simulate a breach and test your team’s decision-making, were either not done or not done well enough.
From a legal standpoint, courts and regulators are increasingly asking whether a company had a reasonable security posture. A plan that has never been tested does not meet that bar. Regular tabletop exercises, updated runbooks, and clear chain-of-command protocols are what “reasonable” actually looks like in a courtroom.
Lesson 5: Forensic Preservation Can Make or Break Your Legal Defense
One of the most overlooked aspects in the response to cyber incidents is digital forensics. When a cyber breach occurs, organizations often want to recover their systems and get back online as quickly as possible. That’s understandable. However, overwriting or rebuilding systems before a proper forensic copy is made can destroy the very evidence that could be used to prove your case in court, or to sue the perpetrator or a vendor whose negligence led to the breach.
The SolarWinds breach is a useful reference point here. Because the attack vector was a supply chain compromise embedded over months, organizations that had good log retention and monitoring were in a far better legal position than those that did not. They could show exactly what was accessed, when, and by whom.
Your cyber incident response plan should include specific procedures for evidence preservation, who is authorized to take a forensic image, log storage, and duration. This is not just a best practice. Should litigation ensue (and it probably will), your chain of custody documents may be the most valuable thing you own.
Lesson 6: Regulatory Landscape Is Moving Fast & Your Policies Need to Keep Up
T-Mobile has now had multiple significant breaches in 2021, 2022, and 2023. Each time, the FTC and state AGs have been watching. In January 2023, T-Mobile disclosed that 37 million customers had data exposed. The regulatory and litigation exposure continues to mount.
What this shows us is that repeat incidents are treated very differently by regulators. This includes the FTC Safeguards Rule, updated HIPAA rules, and new SEC requirements for cyber disclosures. Meanwhile, individual states such as California (CCPA/CPRA), New York (SHIELD Act), Virginia, and Colorado are developing their own frameworks.
This is a patchwork of obligations for a business that operates in many states. Your data governance model must take all of these into consideration. And this must be reviewed at least annually, not just in response to a breach.
One more thing worth calling out: if you’re a publicly traded company, the SEC now requires that you disclose material cybersecurity incidents within four business days after determining that they’re material. If your legal team isn’t involved in the materiality determination process, they should be.
So, Where Does This Leave You?
The common thread in all six of these lessons learned is the same: the technical and legal aspects of cyber incident response cannot be in separate silos. When a data breach occurs, every decision that you make about how to respond to that breach has legal implications.
At Aeren LPO, our cyber incident response review service is built specifically to close the gap between your legal obligations and your actual incident response practice. Because you need to have control before a breach tests everything.